this post was submitted on 17 Nov 2023
12 points (77.3% liked)
Linux Gaming
15825 readers
57 users here now
Gaming on the GNU/Linux operating system.
Recommended news sources:
Related chat:
Related Communities:
Please be nice to other members. Anyone not being nice will be banned. Keep it fun, respectful and just be awesome to each other.
founded 4 years ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
Most malware is written for Windows, especially when it's distributed as a Windows executable. (Almost) no Windows malware targets Wine specifically. However, Wine on its own is not a sandboxing tool, and Windows ransomware will ruin your day.
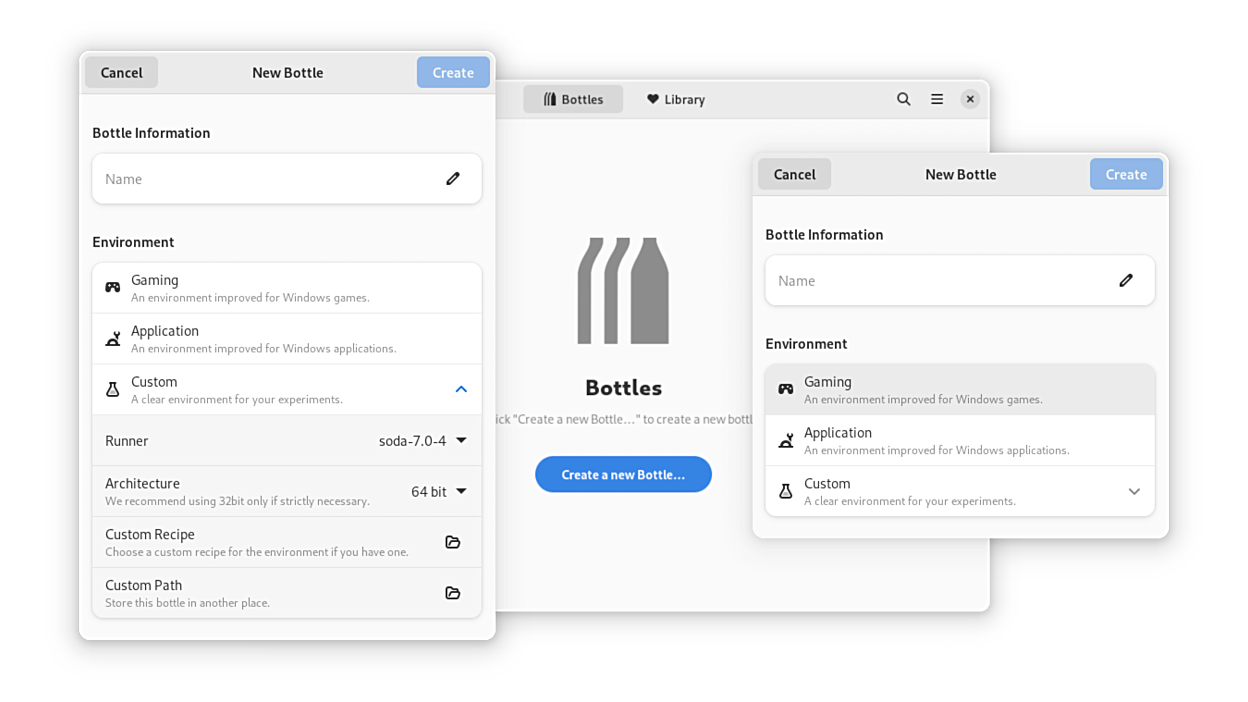
Bottles does two things for security:
By separating wineprefixes, as long as the host filesystem is not directly exposed (which iirc is default for bottles), any malware not written with Wine in mind will only affect its own "bottle".
By being a flatpak, even if some Windows malware specifically targets Wine, it would still have to escape the flatpak sandbox for elevated permissions. If the bottles flatpak has no access to personal files, "Wine-aware" malware won't either.
Although malware can still do damage, even in its own sandbox. For example, botnet type malware would still function. The host system is "safe", but the damage can still be done externally. Usually application-defined "autostarting" of applications is broken under Wine (iirc), which means all non "Wine-aware" malware will only start when an infected windows application is started in bottles.
Any sandbox will eventually be escaped, and malware sophisticated enough will be able to get access to everything on the host system. The chances of running into malware like this in the wild are extremely small.
These are pretty good news! Thank you for explain in a better form the context of situation.
Actually, sounds cool. Now feel sure I can run cs1.6 no steam with 18 trojans detected by VirusTotal from a pakistani server and don't scare me because I will use Bottles into a Arch Linux Virtual Machine lmao (this is just a sarcasm, in any case, I also bought cs1.6. I think there are only hackers anyways)