It's common for people to get these when their email address is similar to my dad's and he forgets his password again.
Mildly Infuriating
Home to all things "Mildly Infuriating" Not infuriating, not enraging. Mildly Infuriating. All posts should reflect that.
I want my day mildly ruined, not completely ruined. Please remember to refrain from reposting old content. If you post a post from reddit it is good practice to include a link and credit the OP. I'm not about stealing content!
It's just good to get something in this website for casual viewing whilst refreshing original content is added overtime.
Rules:
1. Be Respectful
Refrain from using harmful language pertaining to a protected characteristic: e.g. race, gender, sexuality, disability or religion.
Refrain from being argumentative when responding or commenting to posts/replies. Personal attacks are not welcome here.
...
2. No Illegal Content
Content that violates the law. Any post/comment found to be in breach of common law will be removed and given to the authorities if required.
That means: -No promoting violence/threats against any individuals
-No CSA content or Revenge Porn
-No sharing private/personal information (Doxxing)
...
3. No Spam
Posting the same post, no matter the intent is against the rules.
-If you have posted content, please refrain from re-posting said content within this community.
-Do not spam posts with intent to harass, annoy, bully, advertise, scam or harm this community.
-No posting Scams/Advertisements/Phishing Links/IP Grabbers
-No Bots, Bots will be banned from the community.
...
4. No Porn/Explicit
Content
-Do not post explicit content. Lemmy.World is not the instance for NSFW content.
-Do not post Gore or Shock Content.
...
5. No Enciting Harassment,
Brigading, Doxxing or Witch Hunts
-Do not Brigade other Communities
-No calls to action against other communities/users within Lemmy or outside of Lemmy.
-No Witch Hunts against users/communities.
-No content that harasses members within or outside of the community.
...
6. NSFW should be behind NSFW tags.
-Content that is NSFW should be behind NSFW tags.
-Content that might be distressing should be kept behind NSFW tags.
...
7. Content should match the theme of this community.
-Content should be Mildly infuriating.
-At this time we permit content that is infuriating until an infuriating community is made available.
...
8. Reposting of Reddit content is permitted, try to credit the OC.
-Please consider crediting the OC when reposting content. A name of the user or a link to the original post is sufficient.
...
...
Also check out:
Partnered Communities:
Reach out to LillianVS for inclusion on the sidebar.
All communities included on the sidebar are to be made in compliance with the instance rules.
Part of my concern is the email has part of an uncommon spelling of name + some numbers. And that it started all of a sudden, every day. The email is several years old and only now it's begun happening every day.
Have you been pwned?
There's been some new and ginormous data dumps recently.
Maybe it is your time.
I hope you've turned on 2FA.
It is actually safe to ignore them. It means either someone has an email address similar to yours, or a bot of some sort has you email address and only your email address.
Essentially, someone or something goes to the login screen, enters your login, and says "I don't have the password, let me in!".
Sending a code to your email like this is the first step in letting someone in without the password, or more specifically to having them reset it.
Since the email is to check "did you ask for this?", doing nothing tells them that you did not.
If you want some extra peace of mind: https://account.live.com/Activity should show you any recent login activity which you can use to confirm that no one has gotten in.
Also, use two factor, a password manager, and keep your recovery codes somewhere safe. The usual security person mantra. :)
This is all good information and seems well intentioned, but it's worth pointing out in a post about account security that clicking links provided by others and giving it your login information is very unwise (even/especially links in emails like these). For the link you provided, it'd be better to recommend going through a primary microsoft page or login that can be confirmed by the user and getting to the activity history page from there
Also, use two factor, a password manager, and keep your recovery codes somewhere safe. The usual security person mantr
Well, I found the recent activity and none of these were me. At least they all appear to say Unsuccessful sign-in.
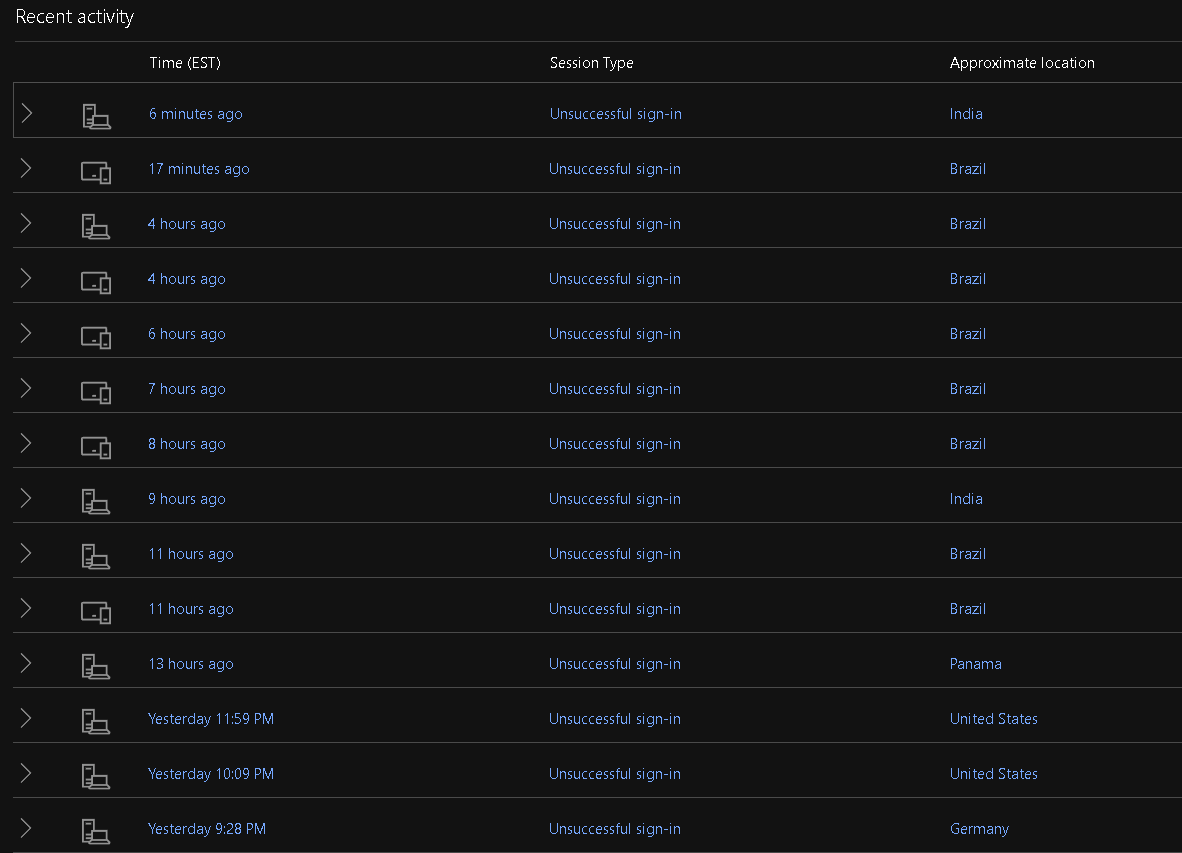
You can create an email alias for your Microsoft account and then only enable login from that account. If you then do not use that email for anything but the login, you should be pretty safe from credential stuffing attacks.
I had a very similar issue with multiple failed login attempts and changing my login email stopped it right away.
Yup, that would indicate that likely a bot is trying to guess it's way in.
You are still safe.
The only weird thing here is that Microsoft lets such things bother you instead of guessing that you didn't teleport to Brazil and instead putting a little extra burden on the Brazil end before sending you an email.
If you're still feeling worried, the biggest thing you can do is enable two-factor auth (which you should do anyway), or even better: enable something like passkeys which are very secure and also easier than username/password.
Two-factor/password manager is the "remember to brush and floss" of the security industry, so... Please do those things. :)
Change your password to something strong, 20 characters plus, and setup 2FA with a 2FA app, google authenticator or Microsoft Authenticator
If you're not using a password manager, now is a good time to start. Bitwarden is free and open source
Use Microsoft authenticator on your account, it won't stop people from trying to access your account but you'll stop getting these and it's generally safer than any kind of email based 2fa
Change your password immediately to something you've never used before and isn't similar to current passwords. If you're getting random 2fa codes, someone is able to complete your first factor, so fix that ASAP.
It might not be 2-factor. Microsoft has an option to log in via email code, which doesn't need a password.
Change your password to a randomly generated password and them setup 2FA
Do not click on anything in the emails as they may be phishing attempts
Just to be clear, change your password by manually typing in the address of the service in question.
Do not use the link in the email to navigate to the service for password changing.
I got one of these emails. It isn't even MFA, nothing to reply with the code to. It doesn't even say which Microsoft account, it sent it to my GMail recovery account. It's so utterly bad not being able to trace the attempt to its source. It's sus that I'm not the only one to have recently experienced this out of nowhere. Maybe it's an attempt to farm valid Microsoft emails from the way this service behaves?
If it happened on a MS account you have, you can check the activity part of the account, it should list all login attempts and give you an IP for each.