Selfhosted
A place to share alternatives to popular online services that can be self-hosted without giving up privacy or locking you into a service you don't control.
Rules:
-
Be civil: we're here to support and learn from one another. Insults won't be tolerated. Flame wars are frowned upon.
-
No spam posting.
-
Posts have to be centered around self-hosting. There are other communities for discussing hardware or home computing. If it's not obvious why your post topic revolves around selfhosting, please include details to make it clear.
-
Don't duplicate the full text of your blog or github here. Just post the link for folks to click.
-
Submission headline should match the article title (don’t cherry-pick information from the title to fit your agenda).
-
No trolling.
Resources:
- selfh.st Newsletter and index of selfhosted software and apps
- awesome-selfhosted software
- awesome-sysadmin resources
- Self-Hosted Podcast from Jupiter Broadcasting
Any issues on the community? Report it using the report flag.
Questions? DM the mods!
view the rest of the comments
Okay...I'm terribly confused by this project here, so maybe you can clarify some things.
First, looking through the code, it seems you're literally just taking input requests and replaying them to a target host. So if Immich is updated with changes that proxy doesn't have yet, everything breaks.
How is this adding more security than any other proxy?
You're correct - it is indeed taking input requests and requesting the related data from Immich.
To allow sharing with Immich using a normal reverse proxy like Caddy or Traefik, you need to expose public access to the Immich
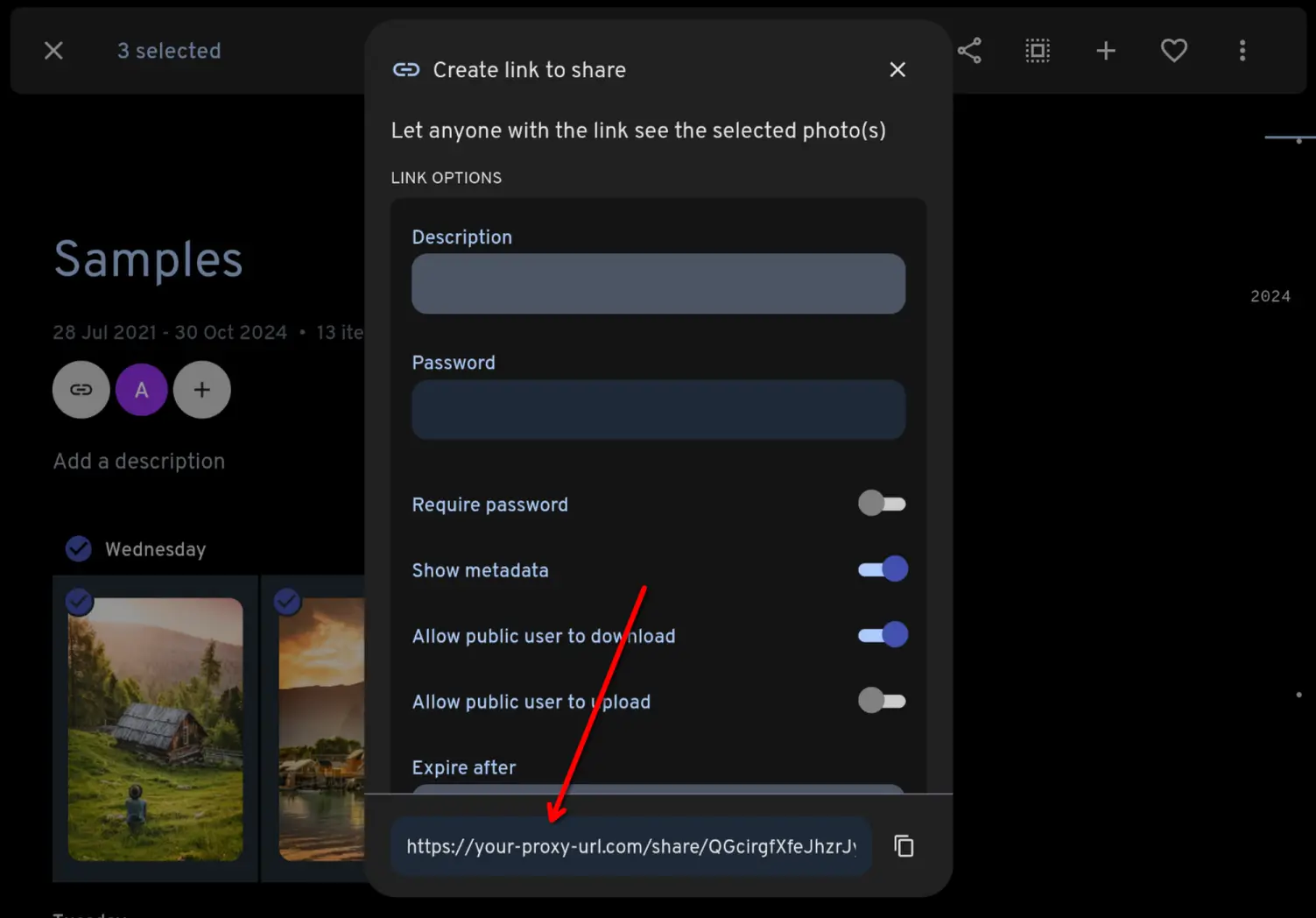
/api/path, along with a few other potentially dangerous paths. Any existing or future vulnerability has the potential to compromise your Immich instance.This proxy is more secure as it does not allow public access to the Immich API path or to any Immich path. The only incoming requests which are honoured are requests like this:
If the shared link does not resolve to something that you have intentionally shared from Immich, it will return a 404.
The only thing which would break it is if Immich changed the format of a few select API endpoints. And if that ever happens it's a very easy fix.
Or you could similar just block those routes in whatever reverse proxy you'd use out in front of the server?
I don't run Immich myself, but just trying to understand the technical issues and this particular solution. Seems like they should have a public facing /shared route that doesn't require access to any others, so I see your point.
You can't. You need to allow public access to your Immich instance's
/api/path to use Immich's built-in sharing.