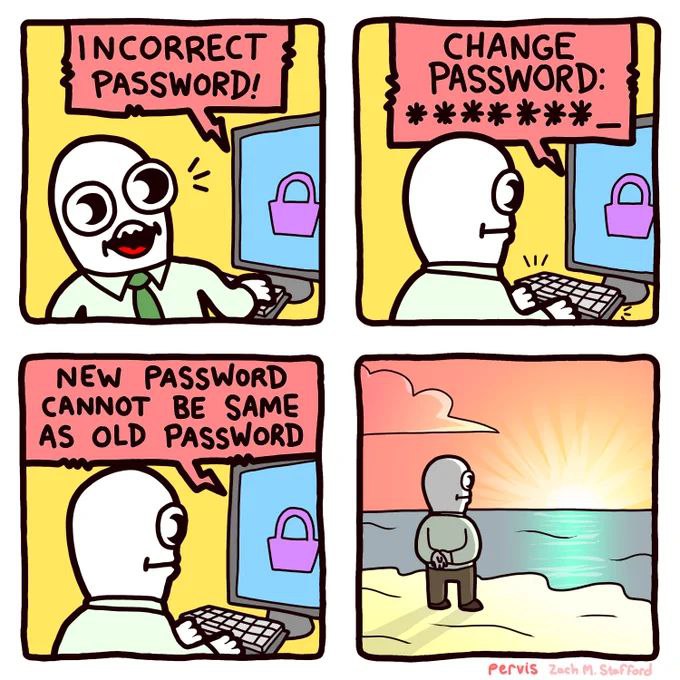
If they just showed the password rules on the login page, this would happen 80% less often to me.
Comic Strips
Comic Strips is a community for those who love comic stories.
The rules are simple:
- The post can be a single image, an image gallery, or a link to a specific comic hosted on another site (the author's website, for instance).
- The comic must be a complete story.
- If it is an external link, it must be to a specific story, not to the root of the site.
- You may post comics from others or your own.
- If you are posting a comic of your own, a maximum of one per week is allowed (I know, your comics are great, but this rule helps avoid spam).
- The comic can be in any language, but if it's not in English, OP must include an English translation in the post's 'body' field (note: you don't need to select a specific language when posting a comic).
- Politeness.
- Adult content is not allowed. This community aims to be fun for people of all ages.
Web of links
- [email protected]: "I use Arch btw"
- [email protected]: memes (you don't say!)
It's so annoying to have to discover the rules one rejected attempt at a time. Worse yet: sometimes you just get vague feedback a la "password contains illegal characters". I usually let KeePassXC generate a safe password for me but in that case I then have to manually permutate the different character classes (numbers, letters, spaces, punctuation, etc) until I find the offender. No good.
If they just showed the password on the login page, this would happen 100% less often to me.
"Password is already taken by user123"
"Your password is incorrect"
"Oooooh..."
Types "incorrect"
that last panel is freaking hilarious
I don't understand what it's communicating. Is he happy? Did he give up on technology, or society altogether?
This'll happen if there's been a suspected data breach with poor password encryption or requirements. Gotta be safe and change the algorithm, breaking everyone's existing passwords. But yeah, it is annoying...
Oh, I thought it had something to do with password hashes, where websites don't actually know your password, but if the hash is the same, then it assumes that you entered the right PW. At least that's how my non-technical brain understands how it works.
That's correct, let's say a database was breached and the hacker has every user and their password hashes. They can login with [email protected] with password "password123" and see if the generated hash matches any other user's password hash. If so, they might be able to hack many accounts with the same password or even reverse engineer and decrypt every other password.
Developers can make the hash more secure by adding arbitrary characters to the password (aka a salt), and this becomes the site's "authentication algorithm". But if the hashes are stolen, it may be a matter of time before the algorithm is figured out, which leads to updates, which leads to your pre-existing hash no longer matching.